
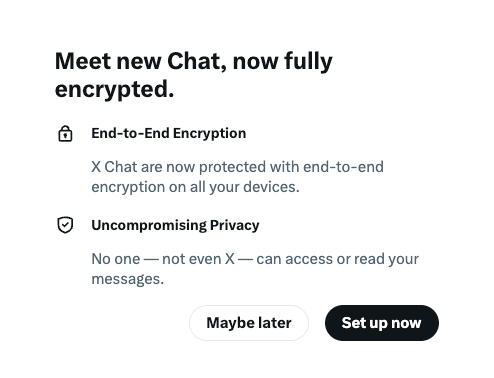
X, the platform formerly known as Twitter, has officially launched its new encrypted messaging feature, dubbed “Chat” or “XChat,” but security experts are urging users to remain skeptical of its true privacy protections.
While the company claims this feature provides end-to-end encryption—ensuring that only the sender and receiver can access message content—cryptography researchers argue the current implementation is significantly less secure than industry standards like Signal.
The Flawed Key Management System
The core of the issue lies in how X handles encryption keys. When users activate XChat, they are prompted to create a four-digit PIN. This PIN is used to encrypt a private key, which is then stored directly on X’s servers. In contrast, services like Signal store private keys exclusively on the user’s local device, preventing the service provider from ever having access to the means of decryption.
Security researcher Matthew Garrett, who analyzed the service during its rollout, notes that without guaranteed use of Hardware Security Modules (HSMs), X could theoretically tamper with or brute-force these four-digit keys. While an X engineer claimed on social media that HSMs are in use, the company has yet to provide public verification, leaving the system in a state of “trust us” security.
Vulnerability to Insider Threats
Perhaps most concerning is the acknowledgment by X itself, documented on their support page, that the service could allow “a malicious insider or X itself” to compromise conversations. This risk of an “adversary-in-the-middle” (AITM) attack effectively undermines the primary promise of end-to-end encryption.
Because X controls the distribution of public keys, users have no way to verify if the company has surreptitiously swapped a key to facilitate eavesdropping. Furthermore, the lack of an open-source implementation—unlike the transparent, fully documented model of Signal—prevents the security community from auditing the code. X has stated plans to open-source the implementation and release a technical whitepaper later this year, but these remain promises for the future.
Missing “Perfect Forward Secrecy”
The service also lacks “perfect forward secrecy.” This essential cryptographic mechanism ensures that each message is encrypted with a unique key. Without it, if a user’s private key is ever compromised, an attacker could potentially decrypt not just current messages, but all historical conversations as well. X has officially admitted to this limitation.
Experts like Matthew Green, a cryptography professor at Johns Hopkins University, remain unconvinced. “For the moment, until it gets a full audit by someone reputable, I would not trust this any more than I trust current unencrypted DMs,” Green stated.
As of now, X has not responded to multiple requests for comment regarding these security concerns.




